Deploying Splunk Universal Forwarders via GPO
When you want to get security event data from your Windows endpoints, there exists a myriad of ways to achieve that objective. Here I am going to outline how to deploy the Splunk Universal Forwarder (UF) using a Group Policy Object (GPO). From there, you can configure the agents using a deployment server to ship the logs to a Splunk Indexer.
These are the general steps we will need to perform to complete this task:
- Download the Splunk UF MSI
- Download the Orca Software
- Create an MST File
- Deploy GPO
Once you have all the software downloaded, install and open Orca first, then from the Orca file menu, select file > open and navigate to where you have the Splunk UF MSI file. After the file loads, select Transform > New Transform. Next, select the ‘Property’ table in the left pane. In the right pane, change the ‘AGREETOLICENSE’ value to Yes.
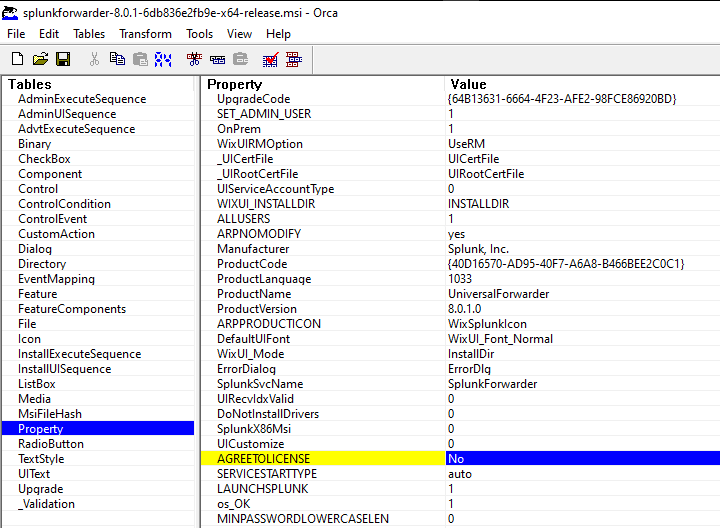
Right-click in the right pane and select ‘Add Row’. The properties that need to be created are:
SPLUNKUSERNAME=splunk_admin SPLUNKPASSWORD=stRongPassword DEPLOYMENT_SERVER=ds.fakelabs.io:8089
If you decide you want to create a domain user then also create:
LOGON_USERNAME=Splunk LOGON_PASSWORD=stRongPassword
The results should look similar to the image below.
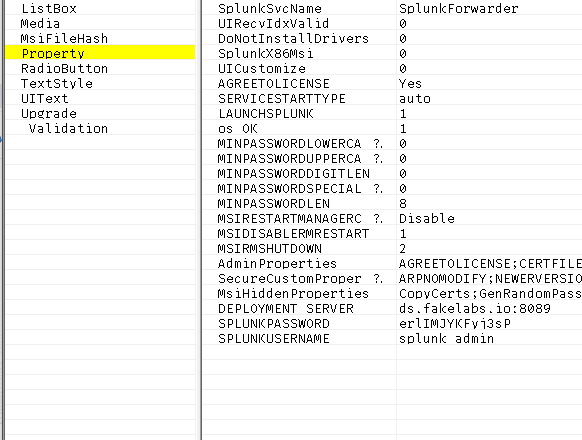
When you are satisfied with the results remember to select Transform > Generate Transform to save the MST file. The MST file that was generated for me was about 20KB.
Keep in mind that you need to protect the credentials in this file since anyone using it can manipulate your forwarders using the management API. I created a Splunk App called disableWebAPI in my git repository that disables this port.
Copy the MST file and the Splunk UF installer to a file share that is accessible by the Domain Controller, and the endpoints that are receiving the software package. Since this is my lab environment, I created a shared folder on my Domain Controller called DeploymentSoftware.
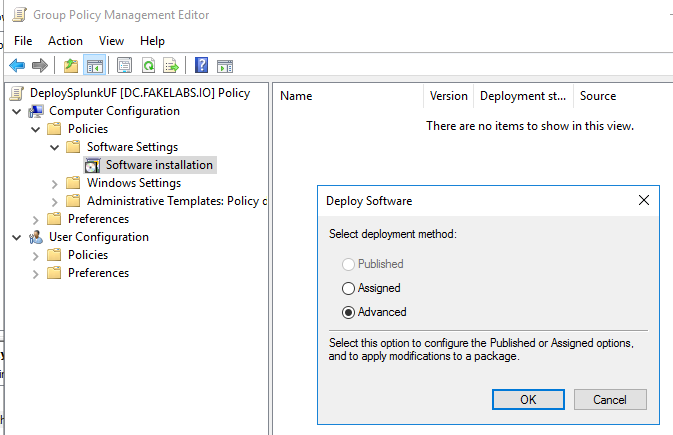
Login to your Domain Controller and use group policy management to create a new GPO, I called mine DeploySPlunkUF. Select Computer Configuration > Software Settings > Software Installation and be sure the radio button for Advanced is selected.
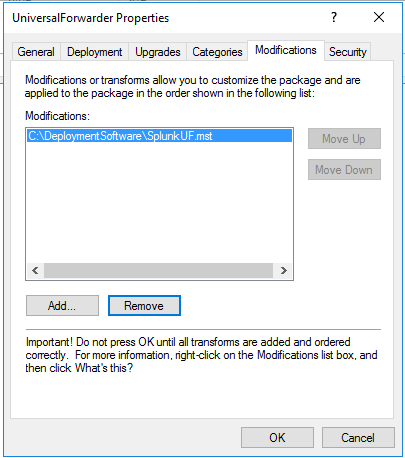
Under the modifications tab select ‘Add’ and navigate to where you copied the MST file. Leave the other tabs at their default values unless you have other operational requirements.
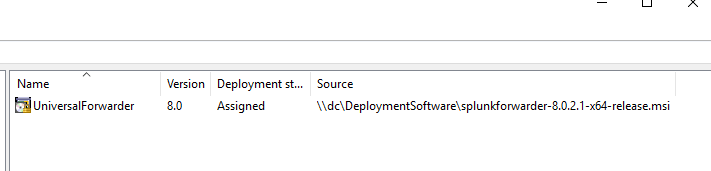
Once you are complete you should see the name of your package and the UNC path to the Splunk UF installer. This UNC path needs to be accessible by all hosts that you intend to deploy the UF on.
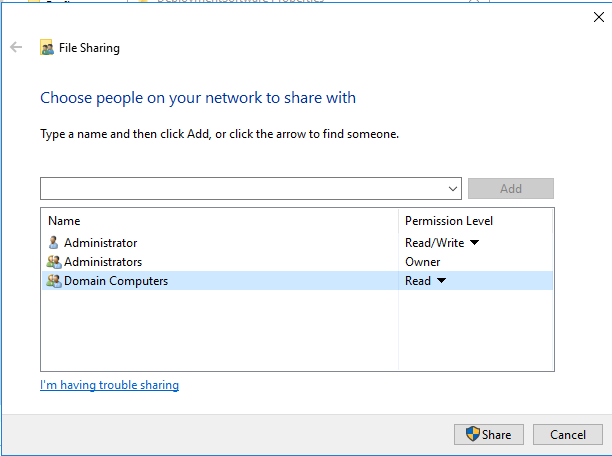
Your file share should have ‘Domain Computers’ with ‘Read’ permissions or the software package will not install. Remember your MST file has unprotected credentials inside so double check your access controls if you decide to have the MST file colocated with the installer.
Copy the GPO to the OU that you want to be affected and when those machines restart the GPO will be applied.
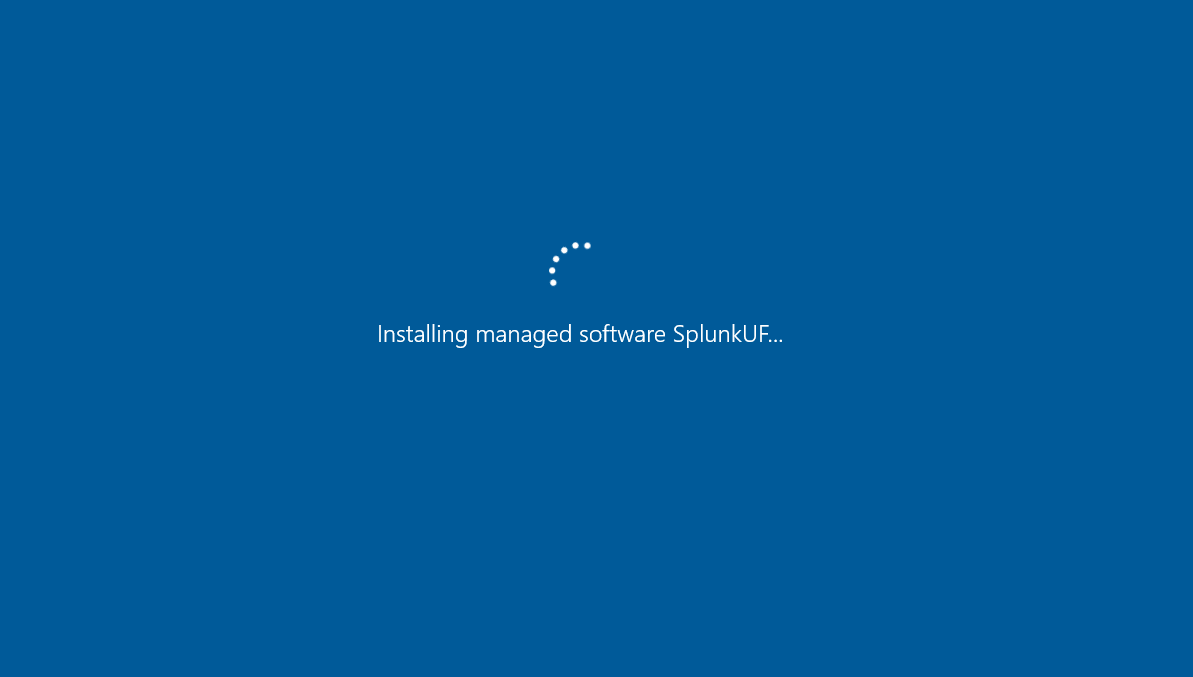
If you do not see the screen in the image above or any screen that delays the login process, then check to see if the UF is installed. If the UF is not installed, then run ‘gpupdate /force’ as an administrator. You should also double-check your permissions on the Shared Folder that contains the Splunk UF.
This came in handy for a site I visited that didn’t have Microsoft System Center Configuration Manager (SCCM) so we had to find an alternate method to deploy the Splunk UF across the enterprise.
Thanks for reading.