Mounting NFS Shares in Windows Using Identity Mapping
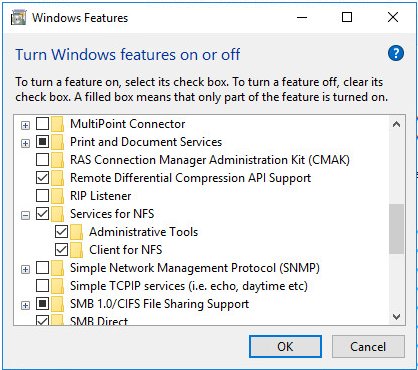
Before we begin let us enable Services for NFS and both Sub Features.
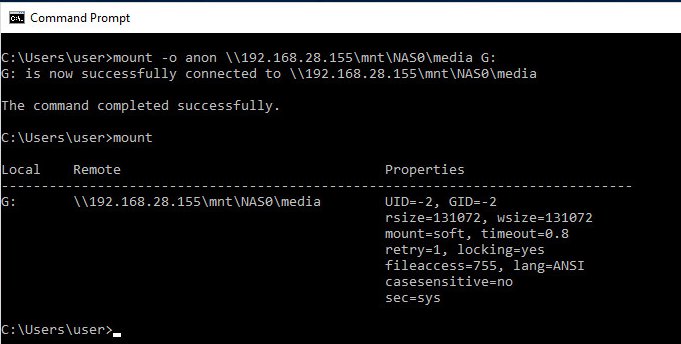
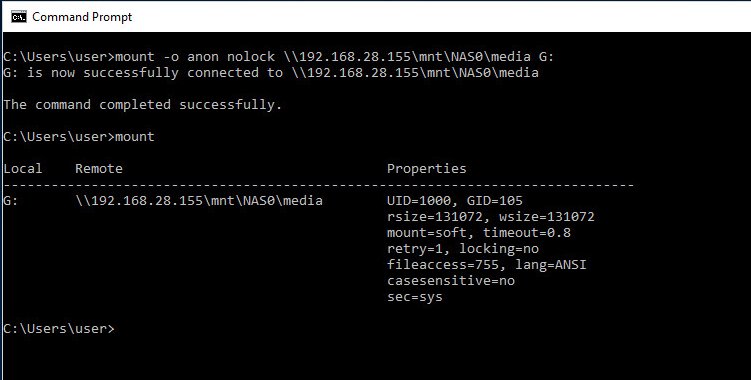
The typical way you will see an NFS share mounted in Windows involves mounting the remote file system using the anonymous (anon) user:
mount -o anon \\192.168.28.155\mnt\NAS0\media G:This will give you read only access based on the configured permissions of the NFS Share.
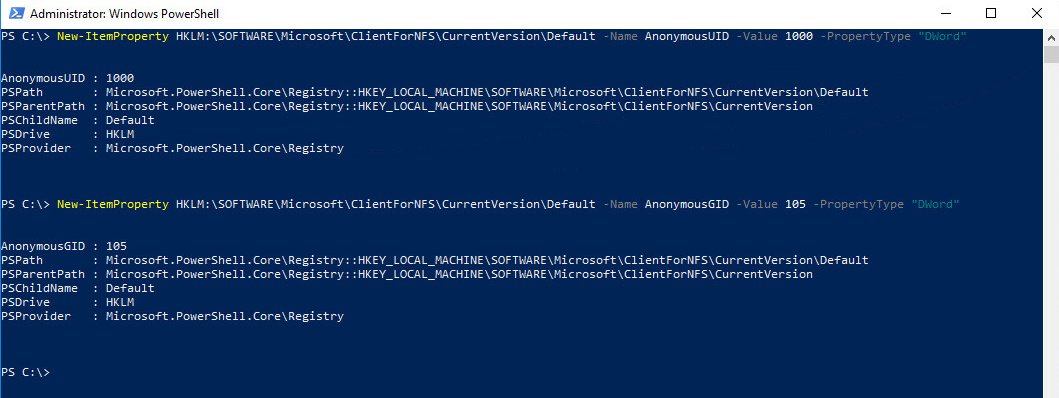
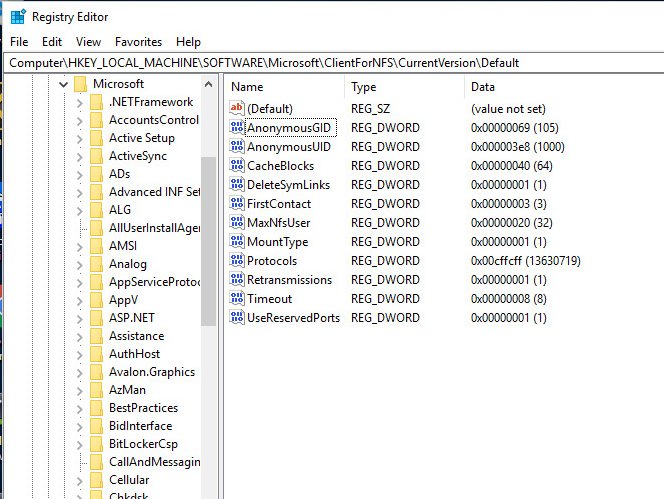
If you want read/write access then you have to add two DWORD Registry Keys with the UID and GID of the Unix user that owns the share. Launch an administrative PowerShell Terminal.
New-ItemProperty HKLM:\SOFTWARE\Microsoft\ClientForNFS\CurrentVersion\Default -Name AnonymousUID -Value 1000 -PropertyType "DWord"
New-ItemProperty HKLM:\SOFTWARE\Microsoft\ClientForNFS\CurrentVersion\Default -Name AnonymousGID -Value 105 -PropertyType "DWord"Reboot.
Restart-Computer -ForceNow mount the NFS Share again
mount -o anon nolock \\192.168.28.155\mnt\NAS0\media G:Most people are apt to stop here since it works. However, any user on the system can mount this share and will have read/write access to that network resource.
In order to enhance our security posture we could use one of several Identity Mapping mechanisms to better secure our interactions with NFS shares. Utilizing the local passwd and group files is one of these mechanisms and does not require an additional server or active directory integration. The location for these files are:
C:\windows\system32\drivers\etc\passwd
C:\windows\system32\drivers\etc\groupThe format should be:
passwd: [domain]\<UnixUser>:x:<UnixUID>:<UnixGID>:Description:C:\Users\<UnixUser>
group: [domain]\<UnixGroup>:x:<UnixGID>:<UnixUID>Here are the contents of both files in my lab VM:
C:\Windows\System32\drivers\etc> type passwd
mechanic:x:1000:100:Windows User,,,:c:\users\mechanic
C:\Windows\System32\drivers\etc> type group
wheel:x:0:0Once these files exist and have valid entries Windows will use them and map permissions to the correct user only. Remove the AnonymousUID/GID registry entries if you created them and make sure you have Services for NFS and the two sub features, Client for NFS, and Administrative Tools enabled.
Then the process is as simple as mounting with the nolock option.
mount -o nolock \\192.168.28.155\mnt\NAS0\media G:If it didn’t work for you double check the following:
- NFS Share UID and GID match what you have in the passwd and group files on the windows machine.
- You have removed the AnonymousUID and AnonymousGID entries in the registry
- You didn’t skip the rebooting part
- When you have the passwd and group files in the correct location you do not use the ‘anon’ option with mount.
Thanks for reading.